In a way, auditing shares similarities with a full-body checkup. While the process is rarely enjoyable, it remains the bedrock of smooth operations and proactive risk management. Central to this effort is security compliance, which requires the cultivation of identity evidence capable of withstanding rigorous examination.
To achieve this level of defensibility, an organization must enforce verification methods and record-keeping practices so resilient that regulators can verify identities with absolute certainty. This state of “audit-readiness” is best realized by aligning internal protocols with regulatory standards, implementing high-assurance identification technologies, and maintaining immutable, tamper-evident records.
The four Ws of audit
The best way to build identity evidence that can withstand rigorous audit scrutiny is providing an end-to-end evidence chain that (a) uniquely identifies a subject, (b) binds that subject to one or more credentials, (c) records authentications and authorisation decisions with sufficient context to reconstruct the four Ws, viz. “who did what, when, where and under what approvals”, and (d) preserves the resulting records with demonstrable integrity, traceability, and retention discipline. Now that we have established what the four Ws are, let us start with the first W: who.
Who?
Who starts with user identity. To underline its importance in an audit, let us look at some commonly used methods, where they fail, and the evidence that needs to be retained.
| Method | What it establishes | Evidentiary strength | Common failure modes | Minimum evidence to retain |
| Basic KYC / documentary checks (manual or automated) | Attributes (name, DOB, address) and documentary plausibility | Medium | Forged documents; weak verification; lack of “why we trusted it” trail | Evidence type, verifier process, checks performed, outcome, operator/system identity, anomaly flags, timestamps |
| Remote IDV + biometric match + liveness/PAD | Link between applicant and an identity document (and/or previous template), plus “live presence” | Medium–High (depends on PAD quality and process design) | Presentation attacks; demographic/quality variability; over-reliance on vendor “pass” | Biometric modality, liveness/PAD method and results, match confidence, device/SDK version, quality metrics, reviewer overrides |
| Knowledge-based verification (KBA) | Claimed knowledge | Low (declining) | Data breaches, social engineering, synthetic identities | KBA questions source category, pass/fail, fallback paths, fraud monitoring evidence |
| Phishing-resistant MFA (passkeys/WebAuthn/FIDO) | Control of a cryptographic authenticator bound to a relying party origin | High for authentication events | Device loss without revocation; weak recovery; poor credential lifecycle inventory | Enrolment/binding event, attestation (if used), key identifiers, AAL mapping, recovery events, revocation handling |
| Password + OTP/SMS MFA | Additional factor over password | Medium | SIM swap, phishing, replay risk; MFA fatigue | MFA factor type, delivery channel metadata, success/failure events, risk signals |
| Hardware-backed signing (HSM + digital signatures) for high-value approvals | Non-repudiation of approval action by a controlled key | High | Poor key governance; shared admin accounts; weak signing policy | Signature, signing certificate chain, timestamp, key custody policy, signing authorization record |
The most effective way to pass the identity test is to clearly define the systems of record, such as HRIS for workforce identities, CIAM for customer identities, and formal registries for privileged and service accounts. In addition, we need to ensure data lineage and ownership are explicit. Without authoritative grounding, downstream evidence loses credibility quickly. The next step is building unified identity visibility, where mature IAM programs still struggle due to fragmented identity signals across environments. This process involves ensuring that authentication events, MFA challenges, privilege elevations, token issuance, OAuth grants, API activity, and session telemetry are normalized and forwarded into a central analytics or SIEM platform. Crucially, identity keys must be consistent across systems. All your efforts will be of no use if identities cannot be correlated end-to-end. Now let us discuss the other Ws (when, where and under what approvals).
About the rest of the Ws
This part can be summed up in one word: logging. Adherence with NIST’s log management guidance, which emphasizes that logs are essential for monitoring, investigation, and operational security, and that effective log management requires policies, infrastructure, and operational processes, will help. The most effective way to prepare identity logging that can easily pass audits is to cover means to access, such as IdP, PAM, or IAM, and the subsequent. To put it, evidence from access to logout; and in case of high-risk actions, the post-action review.
Recommended logging elements
| Field / element | Why auditors care | Typical source(s) | Notes for tamper-evidence |
| event_id (globally unique) | Deduplication and traceability | SIEM, service, IdP | Use ULID/UUID; include source_id + monotonic counter where feasible |
| event_time (UTC) + time_source | Sequencing & correlation | all | Record NTP/PTP source or cloud time sync metadata; monitor drift |
| principal_id (stable) + principal_type | “Who” did it (user/service/device) | IdP/IAM/workload | Avoid mutable display names as primary identity |
| credential_id / authenticator_id | Link to authentication factor | IdP/MFA | Support investigations into factor compromise |
| session_id + correlation IDs | Reconstruct user journey | IdP, app gateway | Ensure propagation across services |
| resource + action + decision | Prove authorisation decision at time | PDP/PEP, app | Store policy version hash/ID for reproducibility |
| source_ip + device posture signals | Context & risk scoring | IdP, endpoint | Treat as personal data where applicable (GDPR) |
| admin_override flags | Explain exceptions | IAM/PAM | Exceptions are likely audit focus areas |
| integrity metadata (hash chain / signature) | Detect tampering | logging pipeline | Use per-batch hashes and signed checkpoints for scalable verification |
Sources: Log management principles from NIST SP 800-92; syslog structure from RFC 5424; and the audit emphasis on policies/procedures and retained logs from PCI DSS Requirement 10. [62]
Key to terminology
- The “Fingerprint” (event_id): Just like a unique case number, this ensures no two events are confused. Using a “globally unique” ID means even if you have millions of logs, you can find the exact one you’re looking for without duplicates.
- The “Timestamp” (event_time): In IT, time is everything. If your server clock is off by even a few seconds, it’s impossible to tell if a user logged in before or after a file was deleted. Using UTC and NTP (Network Time Protocol) keeps everyone on the same universal clock.
- The “ID Card” (principal_id): This is the permanent ID of the person or bot. We use “stable” IDs (like a serial number) instead of usernames because people change their names or departments, but their internal ID stays the same.
- The “Key” (credential_id): This tells the auditor how the person got in. Was it a password? A hardware security key? A fingerprint? This helps prove that the login was secure.
- The “Paper Trail” (session_id): This connects all the different things a user did during one login session. It’s like following a person’s footsteps through a building from the moment they swiped their badge at the front door.
- The “Permission Slip” (resource + action): This proves the system checked the rules before letting someone in. It answers: “Did this person have the right to delete this database at 2:00 AM?”
- The “GPS & Health Check” (source_ip + posture): This records where the person was (IP address) and if their laptop was encrypted and up-to-date (posture). Logging into a bank from a secure office is different than logging in from a public café on a compromised phone.
- The “Emergency Break-Glass” (admin_override): Sometimes admins have to bypass rules to fix a crash. Auditors watch these “overrides” very closely because they are the most common way security is bypassed.
- The “Evidence Seal” (integrity metadata): This is the digital version of a “tamper-evident” seal on an evidence bag. By using hashes or digital signatures, we can prove to an auditor that nobody went into the log file later to delete their own footprints.
Sanket Kadam, Senior Security Analyst at QKS Group, explains, “Identity evidence that withstands audit scrutiny depends on disciplined implementation across the identity stack. Strong Directory & Identity Repository governance, combined with Progressive Profiling and Attribute Governance, establishes a defensible ‘who’ baseline. From there, MFA Coverage and Passwordless Authentication strengthen authentication assurance, while Adaptive / Risk-Based Authentication and Threat Detection in Authentication provide continuous protection against account compromise. Equally important are Policy & Enforcement Models (RBAC/ABAC/Zero Trust) with JIT and Zero Standing Privilege, which ensure authorization decisions are auditable. Finally, resilient Token Lifecycle management, Continuous Session Monitoring, and tight SIEM integration create the end-to-end identity evidence chain that auditors expect from mature IAM programs.”
Preserve To Avoid Disaster During Auditing
This is probably the most anxiety-inducing part of the process. This is because it involves data storing and preservation. These are the areas under the minutest scrutiny by all (increasingly stringent) data privacy laws. Being held noncompliant with the laws means heavy fines and/or loss[SK1] of reputation. Thefeore, retention must be defensible both as “long enough for audit/forensics” and “not longer than necessary” where privacy regimes apply. GDPR’s principles and security obligations make it risky to keep identity logs indefinitely without a purpose/retention rationale, while PCI and healthcare regimes can impose explicit minima for certain records.
A useful step is standardizing templates for auditor-ready evidence. The templates should include access reviews, MFA enforcement, privileged access activity, lifecycle flows, and service account governance. Where possible, logs should be cryptographically verifiable through hashing, immutable storage, or WORM retention. Retention periods must align with regulatory requirements and audit lookback windows, as too many teams discover that critical identity logs were overwritten or aged out prematurely during audits.
Vendor landscape:
Here is a handy landscape that will help you land every W.
| The “Ws” | Functional Category | Vendos |
| Who (Identify) | Identity Verification | Jumio, Veridas, Onfido |
| Who (Bind/MFA) | Workforce/CIAM | Okta, Microsoft Entra, Ping |
| What (Approval/Privilege) | Privileged Access (PAM) | CyberArk, Delinea, BeyondTrust |
| When/Where (Log/Normalize) | SIEM / Identity Analytics | SentinelOne, Splunk, Elastic |
Reference architecture for audit-grade identity evidence
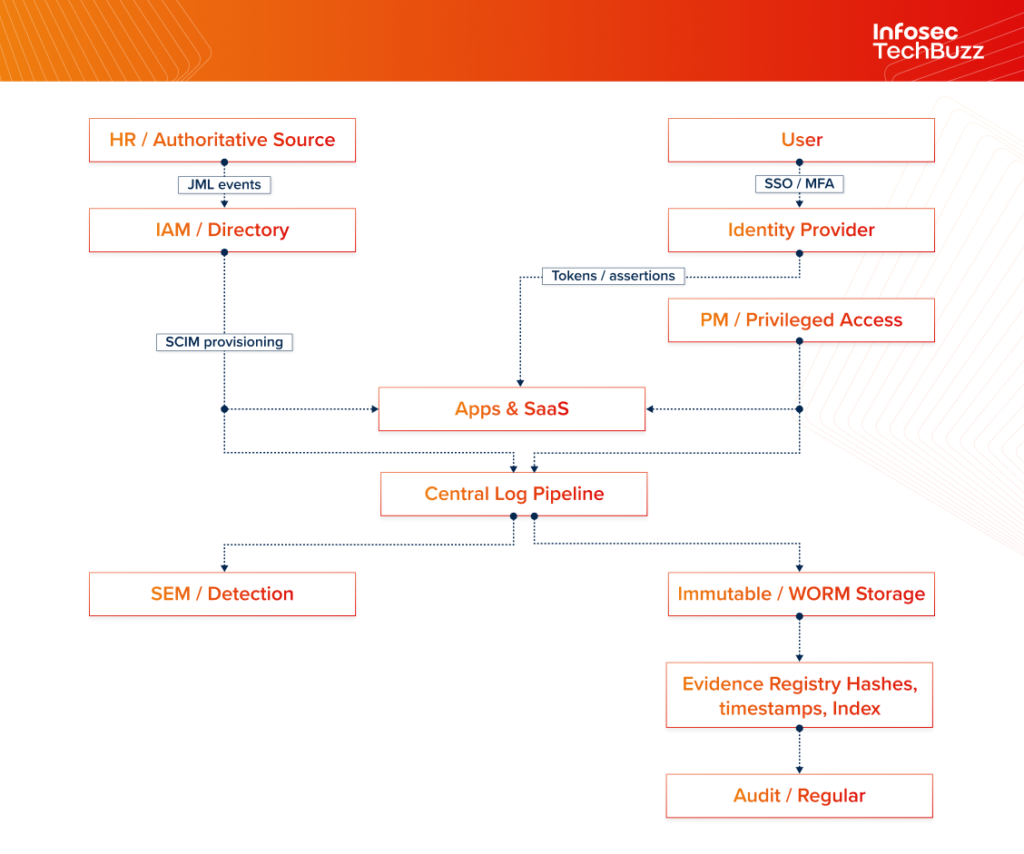
A typical audit-ready architecture separates the identity control plane (IAM/SSO/PAM/provisioning) from the evidence plane (centralized logging, immutable storage, and evidence registry) so that evidence can be produced even when production systems are compromised.