Apart from AI, what is another new thing you can almost certainly find in modern network environments? It is machine IDs. Both share another similarity: careless use and misuse of both will result in absolute disasters. Why? Because, unlike human accounts, machine identities do not benefit from natural security checkpoints. Unlike people, machines cannot leave organizations, change roles, or trigger access reviews. A service account created years ago may still have full access rights, even if the service it supported has been partially redesigned or replaced. From a defense standpoint, this means that access is rarely reduced. Over time, machine identities accumulate privileges that far exceed their original purpose, creating a large and silent attack surface.
Another fact makes the thing scarier. Machine IDs outnumber human users by an order of magnitude. Every cloud workload, microservice, integration, and pipeline introduces at least one such identity. From a security perspective, this scale alone changes the threat model. You are no longer defending a few thousand human users. You are defending tens or hundreds of thousands of autonomous identities that authenticate continuously, without supervision. A juicy target for a bad actor, right? Now, imagine a situation of actual compromise.
Firstly, there will be no alerts. Remember, the ID is valid, and the authentication succeeds exactly as designed. Once the attacker is “in,” he discovers the account has permissions beyond its original purpose. From there, the attacker can enumerate additional resources, extract sensitive data, and invade other systems. And this, again, will not trigger any alarms. All activities will appear as normal application traffic. Worse, logs will also show a trusted service account behaving “normally.” When the breach is discovered, it will be the case of closing the barn door after the horse has bolted and reached the next state.
Longevity is another major pain point. Certificates expire annually. SSH keys persist indefinitely. Secrets embedded in code or configuration files are rarely rotated because rotation risks breaking production systems. Every long-lived credential increases the window of opportunity for compromise. From a security standpoint, it is a certainty that a disaster is inevitable. It is not a question of how or why, but when. It is logical that the longer a secret exists, the more likely it is to leak, be reused improperly, or be discovered by an attacker. Not everyone has the luck of the Golden State Killer.
Speaking of GSK and the lack of enforced visibility, here is more bad news: Many organizations cannot confidently answer basic security questions about machine identities. You know, questions like how many Machine IDs exist in their environments, where they authenticate, what they can access, or whether they are still in use. Without this visibility, threat modeling becomes guesswork. Incident response becomes slower and more uncertain. When suspicious activity is detected, teams struggle to determine whether it is malicious or simply an undocumented system behaving as designed.
Sanket Kadam, Senior Security Analyst at QKS Group, explains, “As environments automate and proliferate, unmanaged machine identity debt quietly expands the attack surface while diluting visibility, ownership, and accountability. Enterprises can materially reduce this exposure by institutionalizing lifecycle management for non-human identities, enforcing least-privilege access, adopting short-lived credentials, and integrating machine identity oversight into identity governance, cloud security, and runtime monitoring. Treating machine identities as first-class citizens of IAM is not optional. It is a strategic control imperative for resilient digital operations.”
Too many Machine IDs are a problem even from a security operations perspective. Machine identity sprawl increases the risk of misconfiguration. Each identity is another policy, role, trust relationship, or certificate that can be incorrectly set. Cloud environments make it easy to unintentionally grant excessive permissions across services and regions. These misconfigurations are rarely caught early because nothing immediately breaks. The security exposure remains latent until an attacker finds it.
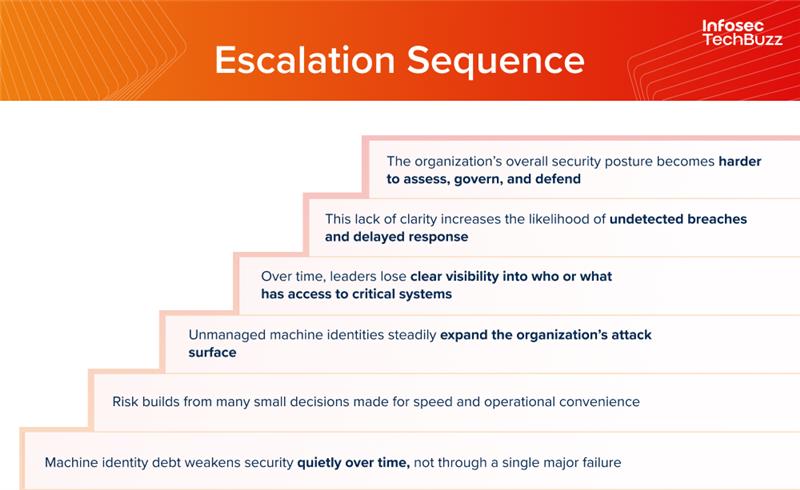
To conclude, what makes machine identity debt especially dangerous is that it erodes security gradually and silently. There is no single point of failure. Rather, it is an accumulation of risk across thousands of small decisions made for speed and convenience. Each unmanaged identity adds more uncertainty, more exposure, and that much less confidence in the integrity of the environment. And one day, things come to a head….Do you want to wait, or do you want to act? If you want to act, here is a handy table laying out the vendor landscape.
| Problem Area | What This Category Secures | Why It Matters for Machine ID Debt | Representative Vendors |
| Machine Identity Management (Certificates & Keys) | Certificates, cryptographic keys, non-human credentials | Long-lived certs and keys are a major source of silent, unmanaged access | Venafi; Keyfactor; AppViewX |
| Secrets Management | API keys, tokens, passwords used by machines | Reduces hardcoded secrets and limits blast radius when credentials leak | Akeyless; HashiCorp |
| Workload Identity & Attestation | Identity for workloads, services, and containers | Replaces static secrets with short-lived, verifiable identities | SPIFFE / SPIRE; Teleport |
| Cloud-Native Application Protection Platforms (CNAPP) | Cloud workloads, permissions, runtime risk | Identifies excessive permissions and risky machine identities in cloud environments | Wiz; Palo Alto Networks (Prisma Cloud); Microsoft (Defender for Cloud) |
| Runtime Workload Protection | Behavior of running containers and services | Detects misuse of legitimate machine identities at runtime | Aqua Security; Sysdig |
| API Security | APIs used by machines and applications | Stolen machine IDs are often abused through APIs that appear “normal” | Salt Security; Traceable |
| Identity & Access Governance (Extended to Non-Humans) | Oversight of access, ownership, and permissions | Helps reduce orphaned and over-privileged machine identities | SailPoint; Saviynt |

