We don’t hate passwords enough. Not only are they required everywhere, but they also need to be complex and unique almost every time. Passkey vaults seemed to be a way out, but they have also turned out to be vulnerable; no wonder more secure alternatives like passkeys are finding increased preference. You do not need to remember zillions of unique passwords, and in case you are using a vault, worry about that vault’s security. But what if you were told that passkeys definitely reduce certain classes of risk dramatically, but do not eliminate identity risk, only shift it upstream? And even if they reduce risk, is there any way to measure it?
Passkeys authenticate through a cryptographic challenge-response tied to device origin and domain. This design directly targets the dominant identity threats of the last decade: phishing, credential stuffing, and password reuse. However, this protection assumes that the endpoint is trustworthy. This is a critical assumption that increasingly does not hold strictly true. Even as passkeys have helped provide protection against various types of attacks, they must face newer types of threats. Endpoint compromise remains a major residual risk. If an attacker gains control of a device through malware, remote access trojans, or supply chain compromise, passkeys offer limited protection. An attacker operating on a compromised endpoint can authenticate using the same passkey, exfiltrate session tokens, or manipulate the authentication flow. In some environments, private keys can also be extracted or abused depending on hardware security module (HSM) implementation, OS protections, and device posture controls. Passkeys assume device trust, and attackers are targeting that assumption.
Session token theft is another emerging threat. Modern applications rely on sessions, cookies, and tokens that persist across devices and networks. Passkeys authenticate users, but they do not protect the session lifecycle. Bad actors can perform token theft via browser exploits, malware, HTML smuggling, or cross-site scripting (XSS). Attackers do not need passwords if they can hijack sessions. Passkeys reduce initial compromise but do little to mitigate post-authentication abuse.
Device loss and shared device environments introduce additional complexities. In unmanaged BYOD scenarios, shared workstations or consumer devices used for enterprise access, passkey trust models become difficult to enforce. Key synchronization across devices, cloud-based key storage, and platform vendor ecosystems introduces new dependency and concentration risks. Identity security increasingly depends on OS vendors, browser vendors, and device manufacturers.
Another emerging area of concern is account recovery processes. Methods like password resets, fallback authentication methods, and helpdesk-based identity verification remain vulnerable to social engineering. As users become less familiar with passwords, recovery processes may force users to increasingly rely on support desks, which are becoming another attack vector, due to the abovementioned vulnerability.
From a market perspective, passkeys have strategic implications for vendors and platforms. Identity providers are integrating passkeys into IAM, SSO, and ZTNA platforms, positioning passwordless authentication as a core control plane. Browser and OS vendors increasingly control key storage and authentication workflows, creating a new layer of platform dependency. Endpoint security vendors become more critical, as device posture becomes inseparable from identity assurance. In effect, passkeys accelerate the convergence of IAM, endpoint security, and browser security into a unified identity stack.
Sanket Kadam, Senior Security Analyst at QKS Group, explains, “Passkeys reduce identity risk, not eliminate it. They are highly effective against phishing, credential stuffing, and password reuse, yet they shift the trust boundary upstream to the device and session layer. As identity risk moves beyond credentials, continuous session monitoring, zero-trust enforcement, and behavioral analytics become essential. These controls help detect anomalous activity, validate device trust in real time, and limit the blast radius of session hijacking that passkeys alone cannot prevent.”
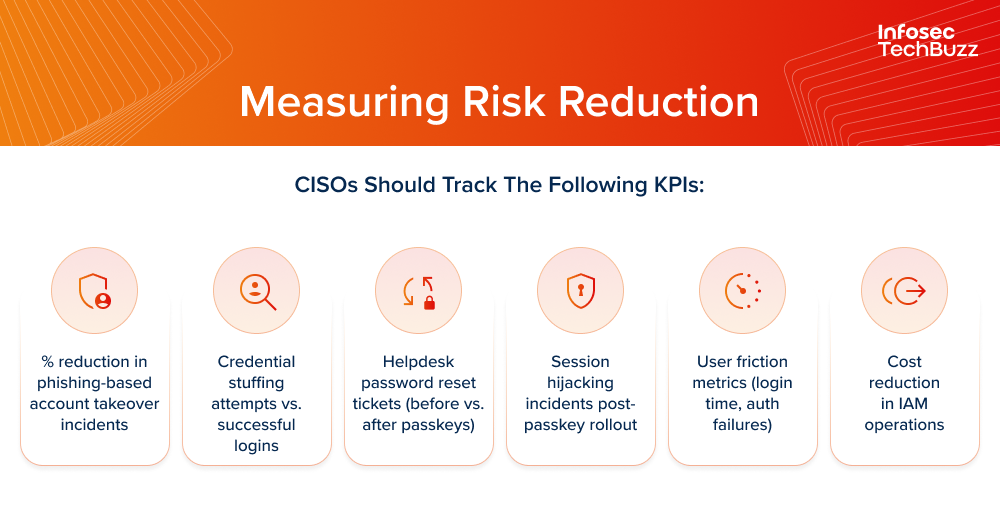
In conclusion, we can safely say that passkeys are not the silver bullet we all dream of. But they can be, when paired with device posture checks, continuous session monitoring, behavioral analytics, and strong endpoint security controls. They do reduce risk, and it is measurable.
Sanket Kadam, Senior Security Analyst at QKS Group, has this advice: “For CISOs, passkeys should be viewed as a foundation, not a finish line. Their impact is best measured through tangible outcomes such as fewer account takeovers, lower credential abuse, reduced helpdesk resets, and improved user experience. When paired with strong endpoint and session controls, passkeys deliver measurable risk reduction.”

